Keysight Launches SBOM Manager to Help Organizations Prepare for Emerging Global Cybersecurity Regulations
Key Terms
software bill of materials technical
sbom technical
firmware technical
vulnerability exploitability exchange (vex) technical
open source technical
supply chain risk management technical
secure-by-design technical
executive order 14028 regulatory
New solution streamlines SBOM generation, vulnerability intelligence, and secure sharing to support compliance with the EU Cyber Resilience Act and global cybersecurity mandates
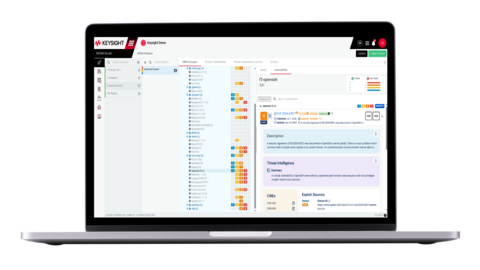
Keysight SBOM Manager enables organizations to generate, manage, and securely share Software Bills of Materials, improving software transparency and supporting compliance with global cybersecurity regulations.
Cybersecurity regulations worldwide are converging on a common expectation: manufacturers must understand, manage, and disclose the components within their digital products, including software and firmware. Regulations such as the EU CRA,
Keysight SBOM Manager is designed to support this shift by addressing the practical challenges organizations face as SBOM requirements expand. The solution enables broader and more accurate visibility into digital products by analyzing binary software, firmware, containers, and other packaged components, including closed-source and deeply embedded dependencies. It continuously correlates SBOMs with multiple authoritative vulnerability sources, intelligently filters out vulnerabilities that are not applicable, and supports the use of Vulnerability Exploitability eXchange (VEX). This enables teams to focus on meaningful risk rather than being overwhelmed by raw vulnerability data.
In addition, Keysight SBOM Manager supports secure and scalable sharing of SBOMs and vulnerability information through controlled, role-based access and version tracking, helping organizations meet regulatory and customer transparency expectations. Built-in validation and normalization help ensure SBOMs align with evolving standards and regulatory minimum requirements, while support for SBOM consumers enables organizations to ingest, manage, and map SBOMs to deployed digital assets, connecting transparency directly to real operational environments.
Naoki Shimazaki, Fourth Design Department, Director, Software-Defined Solutions Division, Connective Engineering Division, Hitachi Industry & Control Solutions, Ltd., said: “The use of SBOMs is becoming an essential element in monitoring system security risks, including software composition management and supply chain risk management. We believe that solutions such as these, which enable visibility into system components and support vulnerability impact analysis, have significant potential to strengthen organizations’ cybersecurity efforts.”
Dmitry Raidman, Co-founder and Chief Technology Officer, CyBeats, said: “While companies innovate at the speed of AI, they must also put tighter governance and stronger controls in place, especially as modern products increasingly rely on open source, third-party components, and AI-assisted development. Supply chain transparency and accountability are now paramount. To meet growing global regulations, organizations need the ability to continuously generate trustworthy SBOMs, correlate them with actionable vulnerability intelligence, apply VEX to reduce noise, and automate response workflows at scale. As transparency expectations expand across software, AI, cryptography, and hardware, visibility into the full digital product stack is becoming essential for secure-by-design development, regulatory readiness, and customer trust.”
Ram Periakaruppan, Vice President and General Manager, Network Test & Security Solutions at Keysight, said: “As cybersecurity regulations mature, SBOMs are becoming a prerequisite for doing business globally. Keysight SBOM Manager helps organizations meet these requirements with confidence by bringing accuracy, consistency, and scalability to SBOM generation and management.”
The EU CRA, which comes into force in 2026, requires manufacturers of connected digital products to implement cybersecurity risk management, maintain SBOMs, and report actively exploited vulnerabilities within 24 hours. Similar expectations are already in place through
By bringing together accurate SBOM generation for digital products, continuous vulnerability intelligence, secure sharing, data quality assurance, prioritization, and consumer-side visibility in a single platform, Keysight SBOM Manager helps organizations reduce regulatory risk, improve vulnerability response, and build greater trust across global digital supply chains.
Resources
- Product Page: Keysight SBOM Manager
About Keysight Technologies
At Keysight (NYSE: KEYS), we inspire and empower innovators to bring world-changing technologies to life. As an S&P 500 company, we’re delivering market-leading design, emulation, and test solutions to help engineers develop and deploy faster, with less risk, throughout the entire product life cycle. We’re a global innovation partner enabling customers in communications, industrial automation, aerospace and defense, automotive, semiconductor, and general electronics markets to accelerate innovation to connect and secure the world. Learn more at Keysight Newsroom and www.keysight.com.
View source version on businesswire.com: https://www.businesswire.com/news/home/20260318019254/en/
Keysight Media Contacts
Andrea Mueller
andrea.mueller@keysight.com
Fusako Dohi
fusako_dohi@keysight.com
Jenny Gallacher
jenny.gallacher@keysight.com
Source: Keysight Technologies, Inc.







